There are a number of variations such as SecDevOps or DevSecOps that have sprung up since the word DevOps started hitting mainstream awareness a few years ago. Cloud, DevOps and MicroServices cheerleaders like Adrian Cockcroft have demonstrated how organizations can transform to take advantage of new digital technologies. What is your take on what DevOps really means? Gene Kim the author of the Phoenix project has published his thoughts in a sequel to his really popular book called Beyond the Phoenix – The Origins and Evolution of DevOps. I have been part of healthy debates at both large organizations and small businesses the evolution of DevOps – is DevSecOps or SecDevOps the right variation to adopt. Clearly the time is ripe to contemplate and explore what’s next after DevOps?
Security and Compliance must be a core to developing and deploying digital assets
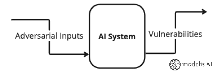
stackArmor’s engineers have been on the frontlines of Cloud Computing and DevOps adoption since 2009 with the deployment of the Recovery.gov System in the AWS cloud. Automation has been the key underlying driver towards delivering accelerated business capabilities using IT. However, numerous cybersecurity breaches and emergence of compliance requirements such as Department of Defense DFARS 7012, NIST SP 800-171 and GDPR underscore the need to address the security backlog. We strongly believe that SecDevOps is right way to think about DevOps because it conveys a SecurityFirst mindset. It is essential that we use proactive and meaningful ways to ensure that the business benefits of IT can be safely delivered to users and consumers. SecDevOps means the incorporation of security best practices into the continuous integration/continuous deployment (CI/CD) pipeline. These discrete activities include static code scanning (SAST) using either open source or commercial tools like Yasca, Checkmarx or similar; dynamic binary scanning (DAST) using solutions like Veracode; vulnerability and penetration scanning using Nessus or similar solutions; and advanced security testing like Fuzzing to detect non-obvious security defects.
The SecDevOps philosophy goes even deeper – we seek to include and integrate the Chief Information Security Officer (CISO) function as part of the development pipeline through automated generation of compliance reports to deliver a more proactive security posture that goes beyond log analysis, monitoring and alerting. Security must be automated and integrated as part of the core development process and not be seen as a “bolt-on” that slows the entire production process. Emerging security and compliance solutions like stackArmor ThreatAlertTM perform dynamic scans that cover the entire stack including user access, application, data, docker containers, operating system and the AWS cloud. The ability generate and produce compliance reports required by HIPAA, FedRAMP, GDPR and NIST security standards as part of the development and deployment process help reduce compliance costs and ensure the confidentiality, integrity and availability of digital assets.
Learn more…
https://stackarmor.com/solutions-2/devops/
https://stackarmor.com/secure-devops-for-fedramp-compliant-cloud-platforms/