The Identity Theft Resource Center states that over 175 million records have been exposed in data breaches in 2015 through October. The incidents of breaches continue to increase and as more businesses are offering SaaS solutions to their customers, SaaS CEOs and Investors must take a careful look at their security practices to avoid business and financial risk.
More and more businesses are offering SaaS solutions to their customers. However, many SaaS firms and their investors underestimate the importance of security as a critical component of their collective success. Many commercial SaaS operators have a “chink in their armor”. The lack of cybersecurity talent, low investment in security tools and generally weak management focus on security issues are contributory factors. This can be a costly mistake.
Changing Regulatory Landscape around Cybersecurity
US Regulators such as SEC and FTC amongst others are starting to aggressively enforce and in some cases expand their jurisdiction to cybersecurity related cases. As an example, in late August, the Third U.S. Federal Circuit Court in Philadelphia ruled against the Wyndham Worldwide hotel chain, stating that FTC has jurisdiction over enterprises and organizations that employ poor IT security practices.
“…Third Circuit Court of Appeals decision reaffirms the FTC’s authority to hold companies accountable for failing to safeguard consumer data. It is not only appropriate, but critical, that the FTC has the ability to take action on behalf of consumers when companies fail to take reasonable steps to secure sensitive consumer information.” said Federal Trade Commission Chairwoman Ms. Edith Ramirez. The FTC’s complaint stated that Wyndham had not followed security measures such as complex user IDs and passwords, firewalls and network segmentation between the hotels and the corporate network. Most of these activities are considered standard operating procedures within most large organizations.
Similarly, the SEC charged an Investment Adviser with failing to adopt proper cybersecurity policies and procedures prior to a data breach when hosting sensitive customer data even though no apparent financial harm occurred. “As we see an increasing barrage of cyber attacks on financial firms, it is important to enforce the safeguards rule even in cases like this when there is no apparent financial harm to clients,” said Marshall S. Sprung, Co-Chief of the SEC Enforcement Division’s Asset Management Unit. “Firms must adopt written policies to protect their clients’ private information and they need to anticipate potential cybersecurity events and have clear procedures in place rather than waiting to react once a breach occurs.”
While data breaches are not new, the SEC and FTC amongst others are starting to take a dim view of poor security practices. Common findings include lack of written policies and procedures; poor operational practices around patching, vulnerability management, continuous monitoring, and lack of encryption of data on disk.
SaaS Cybersecurity should be a CEO and Board level Issue
We at stackArmor have deployed secure and hardened environment for US Federal and large Financial organizations following NIST, FISMA, FedRAMP and HIPAA compliance requirements. However in working with the commercially focused SaaS businesses, we have seen some real challenges that demonstrate a lack of rigor and focus on security. Here are some recent examples:
“”¦while doing cloud hosting cost analysis for a venture funded start-up with $8 million of VC capital, we noticed heavy data egress charges. A simple analysis revealed that a hacker from China penetrated the platform and downloaded the firms’ database and IP”. The vulnerability was traced to an un-patched server.
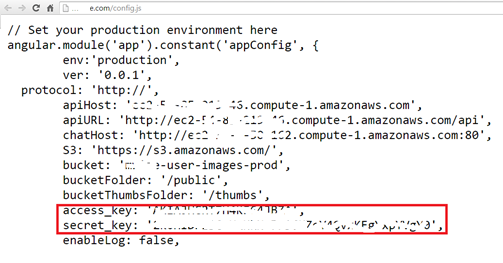
“a SaaS startup exposed their access secret key in their web application in plain view for anyone to access. This could have caused someone to wipe out the firms entire production and operational platform”
“The Technology team of a SaaS startup with Fortune 500 customers is operating their environment in a cloud environment without any intrusion detection and prevention systems such as web application firewalls thereby creating third-party risk.”
What is ironic is that most of these situations can be avoided without spending a lot of money! However, it does require direction from the top – the CEO for a SaaS must set the tone and cannot allow cybersecurity to be “just an IT issue”. Also, as some of the recent FTC and SEC enforcement actions have demonstrated – simply reacting to a breach and “taking care of things” is not an acceptable approach.
SaaS security best practices
A great place to start is the NIST cybersecurity framework which provides a foundation to build upon. In order to avoid nasty surprises, it is important to understand the current state that begins with:
- Completing an information security risk assessment with an executive summary report to identify any deficiencies in administrative, physical, and technical safeguards;
- Documenting current information security posture for executive and technical leadership;
- Defining mitigation activities required to address administrative, physical, and technical risks identified during the risk assessment;
We have developed a simple and easy to develop methodology called ARM, which stands for Assess, Remediate and Manage. The methodology is based on best practices from NIST and the FISMA risk management framework for ensuring the confidentiality, integrity and availability of information systems. Security and compliance is not a one-size-fits-all exercise. Rather, it needs to look at all aspects of the operating environment, to include organizational mission goals, system purpose, user base, and technologies employed.
The assessment and deliverables are tailored to provide added value and relevance to system-unique requirements as well as how systems integrate into organizational operations. The importance of this tailored approach cannot be overstated. A risk assessment, regardless of depth and breadth, will fail to provide necessary direction in meeting a SaaS providers needs for providing an accurate risk and compliance picture unless it is properly tailored to account for the unique offering and environment. Specifically, an inaccurate assessment may lead to unnecessary costs to mitigate a vulnerability that doesn’t actually exist, or may provide leadership with a false sense of security that results in a loss of confidence due to breaches.
The benefits of receiving a security assessment that properly accounts for business objectives, user base, operating environment, and employed technology includes avoiding unnecessary cost associated with “phantom” vulnerabilities and ensuring executive data is protected by applying the right resources, in the right places.
An industry standard risk management and analysis methodology has been developed by the National Institute for Standards and Technology (NIST). The methodology and security controls assessed are drawn from NIST Special Publication 800-53 rev 4, and additionally map to international ISO/IEC 27001/27002 standards to address administrative, physical, and technical security controls. This standard helps provide the foundation for a thorough risk management methodology that includes a tailored risk assessment process, clear and thorough documentation of the risk model, and an approach which ensures repeatability of the risk assessment.
Create A Risk Model
The risk model identifies the risk factors (threats, vulnerabilities, impact, likelihood, and predisposing conditions) to be assessed and defines the relationships among them. A threat is any circumstance or event with the potential for adverse impact to Indiggo operations, assets, or personnel. The source of a threat can be human, environmental, or a structural failure and may be intentional or accidental in nature. A vulnerability is a weakness in an information system, security procedure, internal control, or implementation that may be exploited by a threat source. A predisposing condition is a condition that exists within the organization, its business processes, enterprise architecture, or operating environment that affects the likelihood that initiated threat events result in an adverse impact. The likelihood of occurrence is a weighted risk factor based on the probability that a given threat is capable of exploiting a given vulnerability. The impact of a successful exploitation of a vulnerability or predisposed condition is a measure of the magnitude of harm that could be expected to the SaaS business, its assets, or personnel.
Assessment Approach
Create a hybrid assessment approach that combines the measurable aspects of a traditional quantitative assessment with the flexibility of a qualitative assessment. This provides meaningful risk results that allow for prioritization. In order to provide improved rigor and effectiveness of the risk analysis, use a data driven vulnerability-oriented analysis with clear understanding of impact to provide a more complete and meaningful risk picture that identifies vulnerabilities in policy, process, and technology as well as critical assets and the impact of successful attacks against those assets.
Common Deliverables
Some commonly accepted deliverables from a security and compliance assessment are described in the table below.
Please contact us for free samples of templates for a security assessment and audit or send us an email at [email protected] for a free consultation to assist with your security assessment and vulnerability testing project.
| Deliverable | Description |
| Basic Security Policy | This document provides a basic set of high level security policies that allow client to state that they have a security policy in place that can serve as an initial baseline. |
| Assessment Plan | This is a checklist security assessment, basically a self-assessment with questions asked by an experienced Information Assurance Analyst to demonstrate understanding and maturity of Cybersecurity posture. |
| High Level Security Assessment Report | Security Assessment Report (SAR) that summarizes the scope, approach, and high level findings. |
| Vulnerability and Penetration Testing | Automated scans with basic parameters with provided auto-generated reports. This includes working with the technology team to perform a test to ensure that any technical remediation that have been applied adequately addressed the vulnerabilities found. |
| Attestation Letter | Generally speaking an external third-party should be engaged to execute the assessment and be asked to provide an attestation letter that describes the nature of the assessment, findings and remediation conducted. |



