Security and compliance standards like PCI-DSS, FedRAMP, FISMA, HIPAA and MARS-E 2.0 require strong independent vulnerability assessments and penetration testing. Cloud-based applications hosted on commercial cloud services like Amazon Web Services (AWS) are within scope of such requirements. The manner of testing however requires carefully defining the scope and manner of testing. External Vulnerability Assessments and Penetration Testing is increasingly required to satisfy the requirements of both new regulations like California Consumer Privacy Act (CCPA), GDPR as well as mature standards like FedRAMP, FISMA, HIPAA and PCI-DSS to ensure the confidentiality, integrity and availability of digital information, it is essential to be well informed about vulnerability and penetration testing requirements.
Key to beginning an effective external vulnerability assessment and penetration test is to define the scope and objective.
Scope of Vulnerability Assessment and Penetration Testing
The scope of the testing must be defined and should include specific parameters including whether the focus is the code, the running application or the hosting infrastructure. Also, one must define if accessing or probing administrative functions, privileged user access and management functions are in scope. Normally, the vulnerability assessment and penetration testing are performed against a non-production environment to avoid adverse impact on production operations.
Methodology for Vulnerability Assessment and Penetration Testing
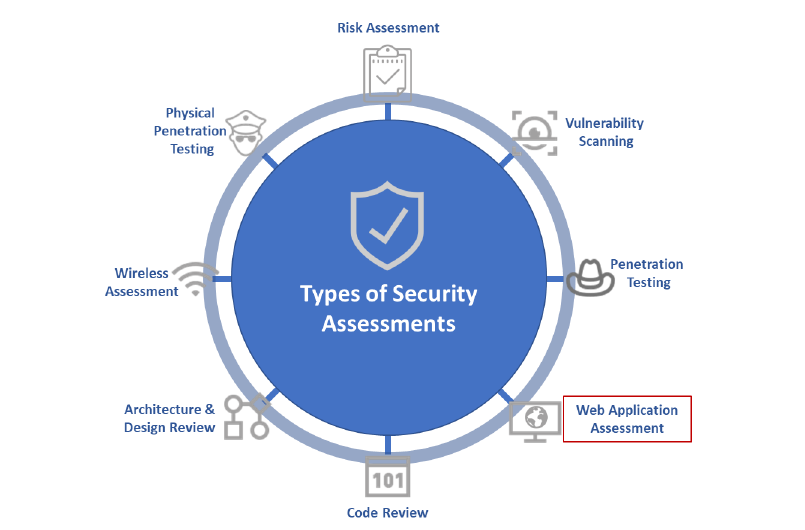
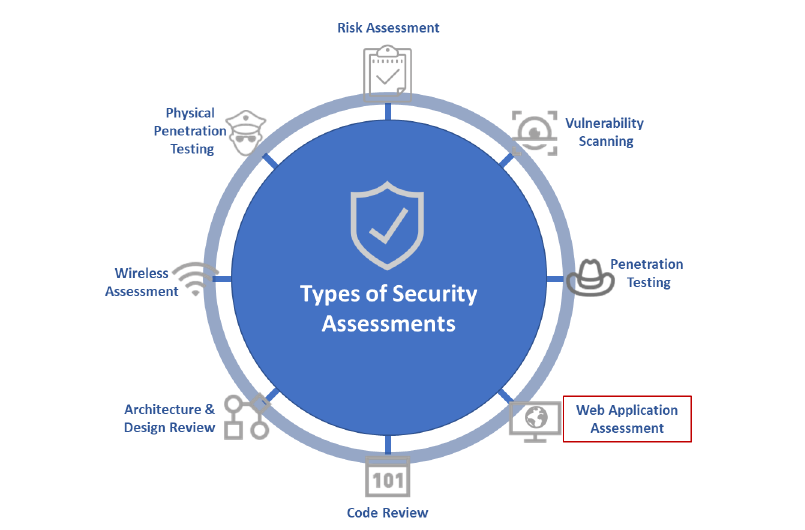
The execution of the vulnerability assessment and penetration testing should follow a standard or well-defined industry best practices. stackArmor conducts its security assessments in accordance with industry best practices, such as:
– NIST’s Technical Guide to Information Security Testing and Assessment (NIST Special Publication 800″115)
– NIST’s Guideline on Network Security Testing (NIST Special Publication 800″42)
– ISECOM’s Open “Source Security Testing Methodology Manual (OSSTMM)
– OWASP’s Testing Guide v3.0
The vulnerability discovery process must evaluate overall system functionality, verify security soundness, identify limitations, and characterize behavior that may lead to system compromise or failure. Identified vulnerabilities should be evaluated and severity ratings assigned based on the NIST 800-30 Risk Methodology.
Automated or Manual Assessment and Testing?
Depending on the size and complexity of a system and the nature of the data processes and stored in the system, organizations must make an informed risk-based decision on whether to conduct a largely automated vulnerability assessment or rely on a more human-based approach. Clearly, automated testing is cheaper, faster and typically will yield “œunknown knowns”. There is a wide variety of scanning tools and technologies including Tenable Nessus, Saint, Metasploit, Brakeman and Burp Suite amongst others. Clearly the tools selected will depend on the nature, scope and depth of the penetration test.
Vulnerability Assessment and Penetration Testing on AWS
All testing and scanning activities performed on cloud platforms like Amazon Web Services (AWS) must follow the established terms of service. This includes requesting for permission to conduct the scanning activity from AWS prior to beginning the scans. Given that the AWS infrastructure is hardened, it is important to identify the scope of the testing relevant for a cloud operator based on the shared security responsibility model. stackArmor has developed a standardized vulnerability assessment and penetration testing methodology that is designed to satisfy SOC2, California Consumer Protection Act (CCPA), GDPR and other compliance and security standards. The stackArmor Security Review Report includes the following key activities:
- Architecture review of the environment including basic AWS account, Region, VPC and IAM services review as well as network segmentation.
- Internal vulnerability scan using the stackArmor ThreatAlertTM AWS vulnerability scanner that rapidly identifies misconfigurations in the environment including VPC, IAM, Security Groups, CIS benchmark practices, Password policy, and security services configuration including GuardDuty and Cloudtrail.
- External penetration scan for detecting common vulnerabilities like cross-site scripting, sql injection and others.
The results are presented in a summarized format. Two rounds of scans are performed – an initial baseline scan and a final remediation scan to ensure changes have been successfully made.