
Lowering FedRAMP, CMMC 2.0 and StateRAMP Compliance Costs is critical for Organizations operating in highly regulated markets with public sector and government clients. Meeting complex NIST 800-53 security control requirements and generating a FedRAMP, StateRAMP, or CMMC 2.0 compliance package are critical requirements. FedRAMP compliance costs can be prohibitive due to the need for R&D, developing a package and implementing FIPS and DISA STIG controls that requires skilled cybersecurity, compliance and cloud experts that understand complex security requirements and government regulations. stackArmor’s compliance accelerator helps reduce the time and cost of FedRAMP, CMMC 2.0, StateRAMP and other Government mandated security requirements by providing a dedicated accreditation boundary with compliant security controls that meet NIST SP 800-53 and NIST SP 800-171 requirements. stackArmor pre-integrated solution delivers an end-to-end technology enabled solution that has been vetted and audited by government agencies, assessors and independent third-parties.
Lowering FedRAMP Compliance Costs with ATO Acceleration
Most government mandated cybersecurity standards such as FedRAMP, DOD CC SRG, FISMA/RMF, StateRAMP, CMMC 2.0 and CISA CPGs can be mapped to NIST SP 800-53 based controls. Most organizations do not have the experience and expertise with implementing security controls-based architectures. ATO Acceleration is a streamlined engineering approach that bakes in security control implementations during the deployment process. The cost and operational savings from the use of ATO Acceleration include:
1) audit-ready dedicated accreditation boundary with NIST compliant security services,
2) complete documentation package with policies, procedures and plans, and
3) integrated security operations, vulnerability management and incident response.
stackArmor’s compliance engineers and cloud architects have developed an “in-boundary” zero trust security architecture that meets all levels of FedRAMP, DOD, CMMC 2.0 and StateRAMP compliance requirements. The ATO Accelerator is a pre-engineered audit ready solution that has security controls implementations directly mapped to NIST SP 800-53 controls families and controls. This avoids the need for organizations to reinvent the wheel by having to perform time intensive gap assessments, reference architectures and traditional advisory services. Most organizations incur cost and time delays by having to research, implement and document security controls from scratch, which can be avoided.
Dedicated Accreditation Boundary
Organizations that operate in highly regulated markets can optimize their operational costs by isolating and securing government data using strong segmentation controls. This pattern is commonly referred to as a landing zone architecture that allows for the separation of user, application and data from the management, and security plane.
stackArmor’s automation pipelines are collectively referred to as ATOM which is short for ATO MachineTM that is part of the ThreatAlert® Zero Trust Security Platform. ATOM leverages and extends the Landing Zone Accelerator (LZA) by using post-deployment hooks to install and configure over 20 discrete cloud-native and in-boundary NIST compliant security services contained within the ThreatAlert® Zero trust Security Platform. The ThreatAlert® Zero trust Security Platform delivers a common set of security services that are available to application tenants that are separated from each other using separate cloud accounts. This separation of workloads by compliance levels allows for organizations to meet the needs of multiple compliance programs including FedRAMP, DOD, CMMC 2.0 and StateRAMP using a single investment.
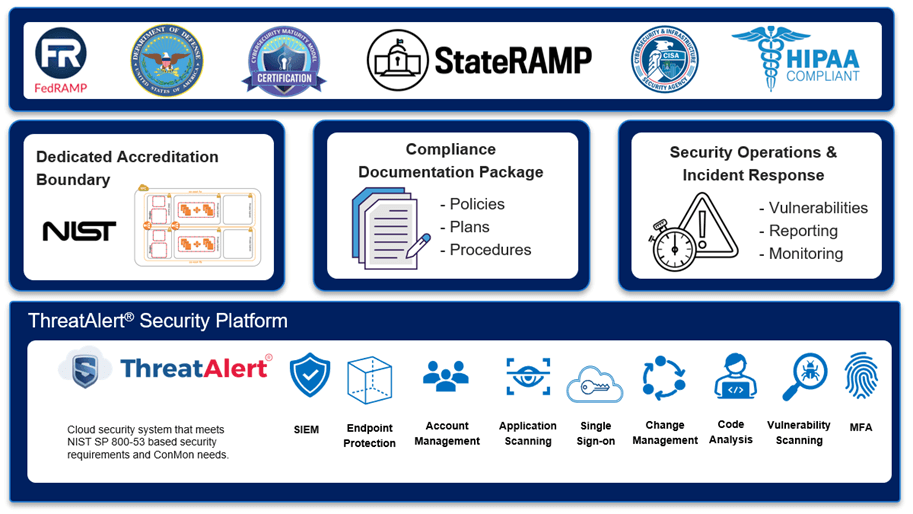
Figure: stackArmor’s ATO Accelerator for multiple government mandated cybersecurity compliance requirements for Organizations in Highly Regulated Industries with Strong Data Sovereignty Requirements
ThreatAlert® Zero trust Security Platform for NIST Compliance
The ThreatAlert® Zero trust Security Platform delivers a common set of security services that are directly mapped to NIST security control implementation requirements. The ThreatAlert® Zero trust security platform components consist of cloud-native and “in-boundary” best of breed commercial security packages that are pre-integrated and vetted for compliance assessments and audits. All security platform components are compliant with FIPS 140-2/3 encryption requirements, have US-based support. The platform supports cloud virtual machines, Kubernetes containers as well as serverless deployments. The security services comprehensively cover the full stack including users, applications, and data as well as the underlying cloud operating platform. The ThreatAlert® Zero trust security platform is OSCAL ready and compliant with NIST SP 800-53 Rev 5 requirements. The security services comply with zero trust architecture requirements mandated by the US Government. Using a pre-integrated platform helps organizations save time and money in researching, evaluating, integrating, testing, and procuring individual security services.
Complete Documentation Package with Audit-ready Controls
stackArmor’s ATO Accelerator leverages cloud-native and “in-boundary” security services that cover nearly 70% of the controls necessary for being assessment ready. stackArmor’s compliance and security architects rapidly tailor and customize the environment to deploy vm-based, container-based or serverless application components based on the clients’ specific needs. The integrated documentation package avoids the use of third-party services and 1099 consultants thereby streamlining the documentation process.
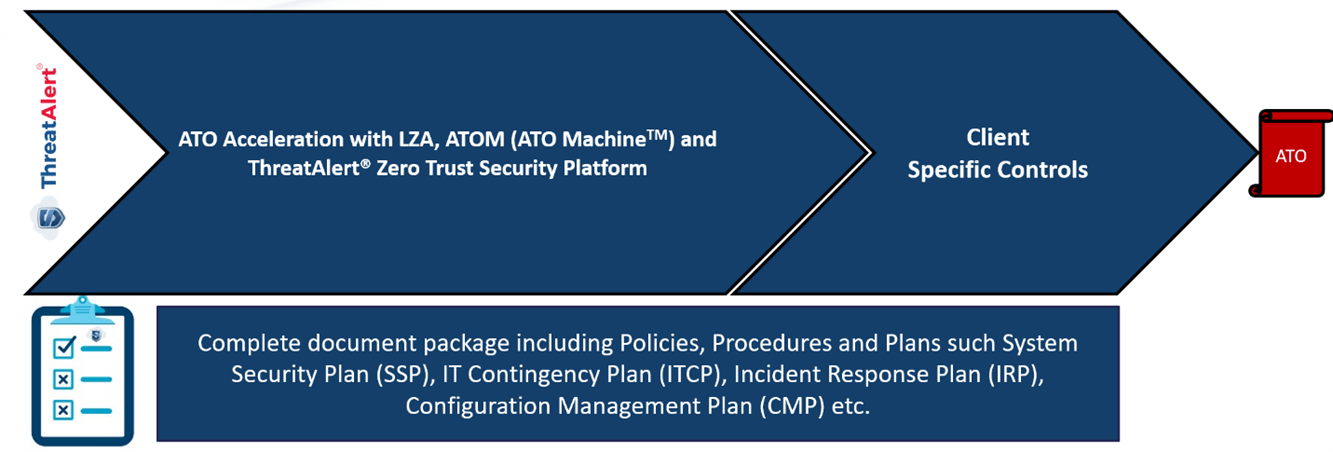
Figure: stackArmor’s ATO Accelerator providing audit-ready control statements, policies, procedures and plans that are over 70% audit-ready helping reduce the time and cost of documentation
Cost-savings with 24/7 Continuous Monitoring and Incident Response
stackArmor helps reduce the need for dedicated staffing by delivering an integrated DevSecOps team of security, cloud and compliance engineers performing continuous monitoring activities. The continuous monitoring service include support for all activities necessary to maintain the ATO status of the system as well as annual re-assessments.
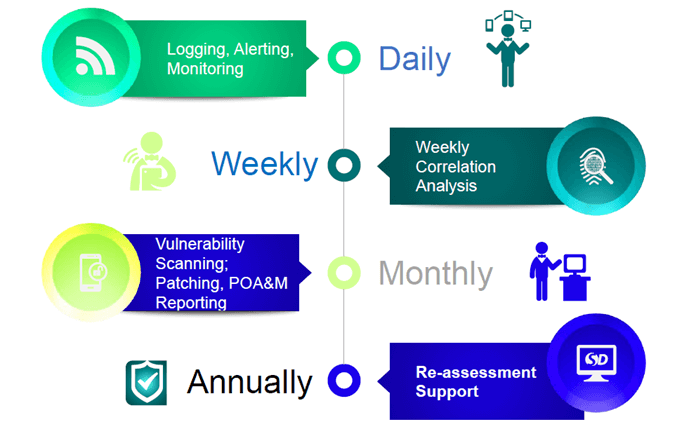
Figure: stackArmor reduces the cost of continuous monitoring and compliance by automating and supporting critical activities including security operations, vulnerability management, incident response and evidentiary reporting as an integrated offering
Compliance Acceleration with ThreatAlert®
Organizations that must meet complex data sovereignty and cybersecurity compliance requirements, can reduce the time and cost of their projects by using audit-ready accelerators. The unique “in-boundary” deployment model dramatically reduces cybersecurity risk as data is self-contained with limited centralization thereby presenting a smaller threat target. By rapidly deploying a sovereign accreditation boundary with pre-engineering security control implementations and audit-ready documentation, most organizations can save between 40% to 70% of time and costs associated with FedRAMP, DOD CC SRG, FISMA/RMF, StateRAMP, and CMMC 2.0 compliance. Please contact us at https://stackarmor.com to learn more about the ThreatAlert® ATO Accelerator and ask for a free ATO-readiness assessment.




