Cybersecurity related regulatory changes are quietly but surely building a tsunami that is going impact every business that conducts transactions online or hosts customer or sensitive data. As the number of data breaches have continued to soar and capture daily headlines, the regulators and lawmakers are forcing changes that will have a significant cost for large and small businesses that ignore the importance of incorporating cybersecurity best practices. This blog is designed to help business leadership with understanding:
- changes occurring in the regulatory landscape,
- impacts on businesses conducting transactions online and
- offers a prescriptive approach to attacking and solving the problem.
Changing Regulatory and Legal Landscape
The past few months have had a stream of non-stop news about high-profile data breaches that have drawn the spotlight on cybersecurity practices across large parts of the US economy. Regulators both at the state and federal level have taken note and have started driving changes through enforcement actions. Here are some seminal cases and enforcement actions that will impact every online business and handles sensitive data.
Aug 2015 – Federal Trade Commission (FTC) v. Wyndham Worldwide Corporation
United States Court of Appeals for the Third Circuit issued a ruling favoring the FTC establishing its jurisdiction in cybersecurity matters and establishing that Wyndham Worldwide failed to take security measures such as complex user IDs and passwords, firewalls and network segmentation, storing sensitive payment card information in clear readable text. Click here to read more.
Sep 2015 – SEC Charges Investment Adviser With Failing to Adopt Proper Cybersecurity Policies and Procedures Prior To Breach
Investment Advisor R.T. Jones was fined $75,000 for storing sensitive PII of clients and others written policies and procedures reasonably designed to safeguard customer information. R.T. Jones failed to conduct periodic risk assessments, implement a firewall, encrypt PII stored on its server, or maintain a response plan for cybersecurity incidents. Even though, R.T. Jones after discovering the breach, promptly retained more than one cybersecurity consulting firm to help analyze the attack. The SEC stated “”¦Firms must adopt written policies to protect their clients’ private information and they need to anticipate potential cybersecurity events and have clear procedures in place rather than waiting to react once a breach occurs.” Click here to read more.
Jan 2016 – Dental Practice Software Provider Settles FTC Charges It Misled Customers About Encryption of Patient Data
Henry Schein Practice Solutions, Inc. the provider of leading office management software for dental practices, agreed to pay $250,000 to settle Federal Trade Commission charges it falsely advertised the level of encryption it provided to protect patient data. Health Insurance Portability and Accountability Act (HIPAA) requires data safeguards. “Strong encryption is critical for companies dealing with sensitive health information,” said Jessica Rich, Director of the FTC’s Bureau of Consumer Protection. “If a company promises strong encryption, it should deliver it.” Click here to read more.
Feb 2016 – California Data Breach Report, Attorney General, CA Department of Justice
The California Department of Justice published a comprehensive report on data breaches reported from 2012 – 2015 that shows retailers, financial services and small businesses as high risk categories for security breaches. The report provides and helps establish a standard of “reasonable security” for customer and sensitive and makes specific recommendations based on established US Federal, and ISO based standards. The report states “an organization that voluntarily chooses to collect and retain personal information takes on a legal obligation to adopt appropriate security controls“. Click here to read more.
March 2016 – Consumer Financial Protection Bureau takes first cybersecurity enforcement action against Dwolla for security practices
The Consumer Financial Protection Bureau took action against online payment platform Dwolla for deceiving consumers about its data security practices and the safety of its online payment system. The CFPB ordered Dwolla to pay a $100,000 penalty and fix its security practices. “Consumers entrust digital payment companies with significant amounts of sensitive personal information,” said CFPB Director Richard Cordray. “With data breaches becoming commonplace and more consumers using these online payment systems, the risk to consumers is growing. It is crucial that companies put systems in place to protect this information and accurately inform consumers about their data security practices.” Click here to learn more.
The Coming Cybersecurity Tsunami – Are you ready?
One of the most difficult problems in the online and IT space is related to establishing a “standard of care” for storing and processing of sensitive information. Recent court and enforcement actions have started to establish that baseline. This is a critical change that impacts business’ cybersecurity related risk and liabilities as measured against this emerging baseline of standards. The NIST Cybersecurity Framework, the Center of Internet Security (CIS) Top 20 Security Controls and regular publications on cybersecurity from regulators are establishing the groundwork for standardizing cybersecurity practices throughout the US Economy. The consequence of not following this new emerging standard and practices is increased liability and risk from cybersecurity incidents and the possibility of punitive enforcement or civil lawsuits.
While none of the cybersecurity prescribed best practices such as use of firewalls, multi-factor authentication and data security are mandatory but the lack such of such practices will have an increasing cost and liability for businesses. The impact likely includes higher business insurance premiums, and higher exposure to legal and liability risk. Also, as the standard of care for cybersecurity is established, many new questions arise. For example in the Franchise business, is the Franchisee or the Franchisor responsible for cybersecurity related risk if the software is mandated for use by all Franchisees? Further, as SaaS models proliferate are resellers responsible and liable to their customers in the event there is a breach at the SaaS providers’ data center?
Clearly, the changing regulatory landscape is changing the dynamic associated with doing business online. Businesses must start educating themselves on cybersecurity best practices, and making the right investments to ensure the integrity of their systems and their brand.
A call to action for SaaS and Online Businesses
As cybersecurity issues become more urgent and important for customers of outsourced IT and software services, compliance with security standards such as ISO 27001 is expected. Most buyers of hosted solutions are looking for ways to contain third-party risk. It is critical for cloud platform operators to have a formal compliance program to contain business liability and risk as well as ensure the ability to attract security conscious customers.
SaaS and cloud platform operators should put in place a formal compliance program that is right sized for their business. At a minimum the following activities should be performed:
- Create a risk model through an information security risk assessment identify deficiencies in administrative, physical, and technical safeguards;
- Document current information security posture for executive and technical leadership to assure compliance with emerging standards and regulations;
- Document mitigation activities required to address administrative, physical, and technical risks identified during the risk assessment;
Create a Risk Model
The risk model identifies the risk factors (threats, vulnerabilities, impact, likelihood, and predisposing conditions) to be assessed and defines the relationships among them. A threat is any circumstance or event with the potential for adverse impact to operations, assets, or personnel. The source of a threat can be human, environmental, or a structural failure and may be intentional or accidental in nature. A vulnerability is a weakness in an information system, security procedure, internal control, or implementation that may be exploited by a threat source. A predisposing condition is a condition that exists within the organization, its business processes, enterprise architecture, or operating environment that affects the likelihood that initiated threat events result in an adverse impact. The likelihood of occurrence is a weighted risk factor based on the probability that a given threat is capable of exploiting a given vulnerability. The impact of a successful exploitation of a vulnerability or predisposed condition is a measure of the magnitude of harm that could be expected to the firm, its assets, or personnel.
Adopt an Assessment Approach
There are numerous assessment options that include finding the right partner(s) for conducting the assessment. For many firms (especially smaller ones) A hybrid assessment approach is one that combines the measurable aspects of a traditional quantitative assessment with the flexibility of a qualitative assessment is ideal. This provides a great starting baseline for organizations that do not have an established cybersecurity and risk management program. Any assessment should cover the following elements:
- full-stack technical architecture including application, data, operation system, hosting environment and shared responsibility model of cloud service provider,
- operations framework including continuous monitoring, vulnerability management, access management, and disaster & incident management
- policies, procedures and tools necessary to execute a meaningful and manageable cybersecurity risk management program
An experienced cybersecurity compliance and security architecture service provider can typically provide complete coverage and provide a meaningful assessment. In the event a formal certification is required e.g. for PCI-DSS, HIPAA or FedRAMP compliance, a third-party assessment organization that is approved to perform accerditations may need to be hired.
stackArmor A.R.MTM – Assess. Remediate. Monitor.
Based on years of experience in performing Security Accreditation & Authorization (SA&A) projects for US Federal and Department of Defense customers, stackArmor has developed a simple and easy to understand overlay that sits on top of NIST cybersecurity standards and guidelines. stackArmor A.R.MTM (Assess.Remediate.Monitor.) is designed to help organizations and key stakeholder quickly and easily understand and act on improving their cybersecurity posture. Most current cybersecurity frameworks are designed for seasoned Information Technology and Information Assurance professionals and thus difficult to help create wider awareness. A.R.MTM is a common sense approach that provides organizations with an implementation framework to adopt the right set of security controls relevant to their business and industry. The methodology and security controls assessed are drawn from NIST Special Publication 800-53 rev 4, Center for Internet Security 20 Security Controls and ISO/IEC 27001/27002 standards. The Exhibit 1 below provides an overview of the stackArmor Cybersecurity Risk Management framework that includes Assess.Remediate.Monitor phases.
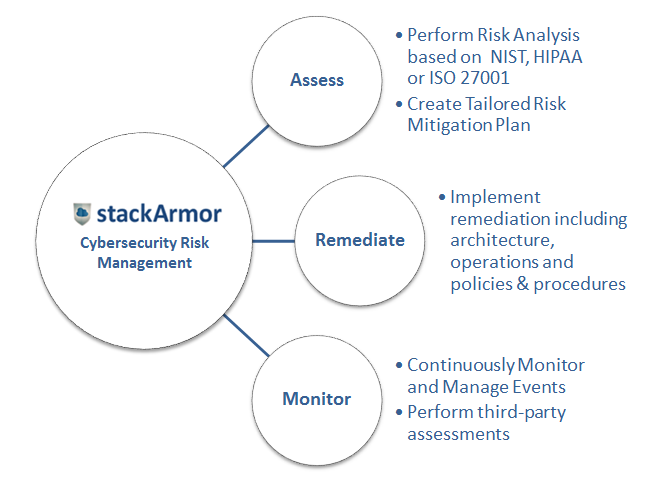
Exhibit: stackArmor Cybersecurity Risk Management Framework for Online businesses
Documents and Deliverables
Following is a complete list of all project deliverables that help in creating a tangible compliance model and framework for a typical organization. Typical documents and deliverables produced at the end of a compliance project are provided in the table below.
| Document | Description |
| Basic Security Policy | This document provides a basic set of high level security policies that allow client to state that they have a security policy in place that can serve as an initial baseline. |
| Assessment Plan | This is a checklist security assessment, basically a self-assessment with questions asked by an experienced Information Assurance Analyst to demonstrate understanding and maturity of cybersecurity posture and procedures. |
| High Level Security Assessment Report | Security Assessment Report (SAR) that summarizes the scope, approach, high level findings and recommendations. The high-level recommendations are for any security controls found to be “not in place” and include description of actions necessary to show the security control is “in place”. |
| Vulnerability and Penetration Scanning | Automated scans with basic parameters with provided auto-generated reports. This effort will includes working with the hosting platform provider to understand the boundaries of the shared responsibility model. A remediation test must be conducted after the initial findings have been resolved. |
| Letter of Attestation | Executive summary of assessment signed by an experienced and certified Cybersecurity Specialist. The letter will attest to the overall level of risk (Low, Moderate, High) based on the security controls found to be “not in place” and it will include a reference to the methodology utilized to categorize the system being assessed, selection of security controls assessed. |
About stackArmor
stackArmor is a cybersecurity, cloud architecture and technology services firm with expertise in meeting the needs of regulated and compliance oriented markets such as Federal and Commercial clients in Financial Services, Healthcare and Defense. stackArmor’s Cybersecurity and Information Assurance professionals have successfully performed multiple large security compliance and vulnerability assessments especially in cloud environments such as AWS Amazon Web Services). We have worked with multiple standards including NIST, FISMA,FFIEC, FedRAMP, HIPAA and ISO 27001. The Cybersecurity and Information Assurance practice is staffed with certified and experienced practitioners with industry certifications such as Certified Information System Security Professional (CISSP) as well as a Certified Information Security Manager (CISM). Learn more by visiting https://stackarmor.com or send us an email at [email protected].
Schedule a free cybersecurity risk assessment with a stackArmor Information Assurance Specialist by contacting us or sending an email to [email protected].



