Magento is an open source cloud based digital commerce platform that empowers merchants to integrate digital and physical shopping experiences. Magento enterprise edition provides an engaging shopping experience to the users by providing personalized content, fast checkout and a seamless shopper experience. However, in order to ensure the integrity of the user experience and sensitive customer data, it is important to follow security and deployment best practices. stackArmor’s cybersecurity and cloud deployment experts have developed a proven and full-stack methodology to help protect and secure applications and data.

Additionally, it is important to follow Magento specific guidelines for creating a secure eCommerce platform that is compliant and protected.
- Keep Magento and Extensions Up to Date: It is very important that you are always running the latest version of Magento as updates generally contain security fixes. It is also very important to keep your Magento extensions up to date.
- Strong Usernames and Passwords: Commonly mistakes in selecting usernames and passwords is to use easy to guess patterns like using “admin” as your username. Always use non-obvious usernames and strong passwords.
- Two-Factor Authentication: Given the number of breaches that occur due to weak passwords, installing a 2-factor authentication mechanism that uses a cellphone or email as an additional verification service for executing important user functions.
- Block Bad Bots: There are always bad bots, scrapers, and crawlers hitting your Magento sites and stealing your bandwidth. You can see a comprehensive list of bots at botreports.com. Many of the security extensions mentioned above can work great to block bad bots, but sometimes you might need to do this at the server level. If you wanted to block multiple User-Agent strings at once, you could add the following to your .htaccess file.
- File Permissions: To protect your Magneto shop you want to make sure and use the correct file permissions. Each directory and file has different permissions which allow people to read, write and modify them. If your permissions are too loose this could open up a door for an intruder and if they are too restrictive this could break your Magento install as extensions and the Magento installation need to be able to write to certain directories. Magento has some great documentation on setting privileges and ownership after you install Magento. For example, lock Down local.xml File. It is also important to note that the local.xml file, located in app/etc/local.xml holds all of your database connection and should be configured with restricted access with file-s permissions to 600, or (-rw——-). These permissions restrict read-and-write access to your user alone.magento local xml file
- Custom Path for Administrator Login: Changing the default admin and login pages can help deflect common attacks. To change the admin path in Magento, go to the app/etc/local.xml file, find the line with this code: <![CDATA[admin]]>, and change the string admin to the required admin string. For example, if you want to change the admin panel URL to https://your -magento-site.com/backdoor, change the CDATA code to <![CDATA[backdoor]]> . You might also want to change the path for Magento Connect Manager, as this is another entry point for hackers.
- Restrict Admin Access by IP Address: You can also restrict access to your admin area by IP address by using the following in your .htaccess file.
- Hardened Hosting Enclave: Installing adequate network level protection using a Firewall is critical including Intrusion Prevention and Detection (IPS/IDS) & Web Application Firewall (WAF).
- Enforcing Operational Hygiene: Applying continuous monitoring and logging of critical security events such as failed login attempts, patching the operating system, data and application servers as well as ensuring adequate level of backups of critical data are common activities.
Configuring Amazon Web Services (AWS)
Amazon Web Services provides the necessary infrastructure support for a secured deployment of Magento E-commerce platform. The process of deployment is highly scalable, cost effective and highly flexible. The AWS infrastructure takes up the responsibility of the operational security of the system, the user takes up the responsibility of the guest operating system.
The following steps should be executed to ensure a well architected solution.
- An Amazon VPC with three subnets in multiple availability zones
- A network translation instance deployed in the public subnets and configured with an Elastic IP address for out bound internet connectivity and inbound SSH access
- A MySQL database engine deployed via Amazon RDS
- Elastic Load balancing to distribute traffic across multiple web server instances
- Amazon EC2 web server instances launched in the private subnet
- Auto scaling to automatically increase the capacity if there is a sudden increase in the demand.
- AWS Identity and Access Management (IAM) instance role that define access to AWS web services
- Security Groups to restrict access to the various protocols and ports
The diagram below provides an overview of the hosting configuration using multiple availability zones and micro-segments using private and public subnets.
Turbo-charging Magento with AWS Aurora
Amazon Aurora is a MySQL-compatible relational database engine that combines the speed and availability of high-end commercial databases with the simplicity and cost-effectiveness of open source databases. Amazon Aurora provides up to five times better performance than MySQL with the security, availability, and reliability of a commercial database. AWS Aurora provides a high-performance database engine for Magento with a significant performance boost and reduced total cost of operations for large systems. Key highlights of AWS Aurora for Magento deployments include:
- MySQL 5.6 compatible
- 5X throughput of MySQL 5.6
- Single digit milliseconds replica lag time
- No modifications required to MySQL apps
- Hot failover for up to 15 read replicas
- Self-healing and fault tolerant storage
- DB storage auto scales to up to 64TB
- Easy to provision via AWS console
AWS Aurora offers 2 times the throughput of MySQL per node in real-world tests published by Magento with 20 rps (MySQL) vs. 40 rps (Aurora). The Replica lag on Aurora is critically lower vs. Master-to-Slave MySQL configuration with AWS Aurora < 40-100ms vs. MySQL > 500ms.
AWS Aurora pricing options are provided below for US East On-Demand rates. Associated storage is charged at $0.10 per GB and other charges per request apply.
| AWS Aurora Instance | vCPU | Memory (GB) | Hourly Cost | Monthly with 100% Utilization |
| db.r3.large | 2 | 15 | $0.29 | $215.76 |
| db.r3.xlarge | 4 | 30.5 | $0.58 | $431.52 |
| db.r3.2xlarge | 8 | 61 | $1.16 | $863.04 |
| db.r3.4xlarge | 16 | 122 | $2.32 | $1,726.08 |
| db.r3.8xlarge | 32 | 244 | $4.64 | $3,452.16 |
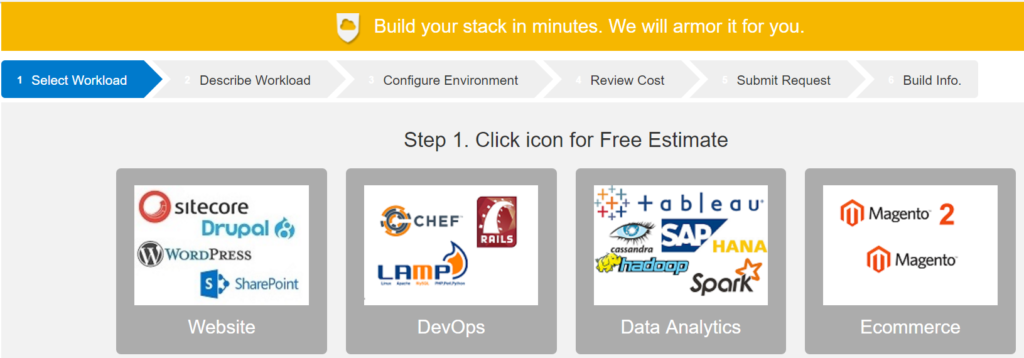
Ready to get started with Magento on AWS? Start with a free estimate with StackBuilder https://stackbuilder.stackarmor.com
Are you interested in secure hosting on AWS and avoiding common mistakes?



